Hello everyone! Over recent years, we have seen how web applications had embraced the use of two-factor authentication (2FA) to better protect their users. This is a good trend. Having 2FA certainly raise the authentication security to a much higher level. However, while 2FA is effective against brute-force attacks, it is not foolproof against phishing attempts.
If you have do not know what a phishing attack is, do refer to one of my older posts to understand more. These days, phishing attacks are getting increasingly sophisticated. This article illustrated 2 case studies on how fake sites could look so real that they were enough to trick users to enter their 2FA one-time password. The fake sites would then store and forward those credentials to login immediately on the actual sites.
Reason for Weakness
Most 2FA relies on one-time passwords (TOTPs) that are time-based. How TOTPs work is to have the server and user device (can be your phone or other tokens) calculate the OTP based on the current time. The user device and server would have already shared a key in advance which will be used as part of the calculation. As long as both the user device and server get the same value for this period of time, the OTP is valid. More info on TOTP can be found from Wikipedia.
Because the key was shared in advance and there is no further verification done by the user device on the server, the authentication process will be susceptible to phishing attacks. As per the article, cleverly crafted phishing sites will be able to steal the login password plus the OTP and login in real-time. The victim may not even know what happened.
Mitigation Techniques
The best way to mitigate such phishing attacks is to allow users to verify that the OTP request is from the server/application that he/she is trying to login. Rightfully, users should check the SSL certificates on the websites to validate the authenticity of the site. However, not all users will do that. As a result, for better user experience and security, the onus is then on the website owners to provide an easy way for users to validate authenticity.
Companies with sufficient funds can invest in infrastructure and separate mobile apps. Some implementations send SMS OTPs with additional verification codes to users so that they can verify the origin. An example as below:
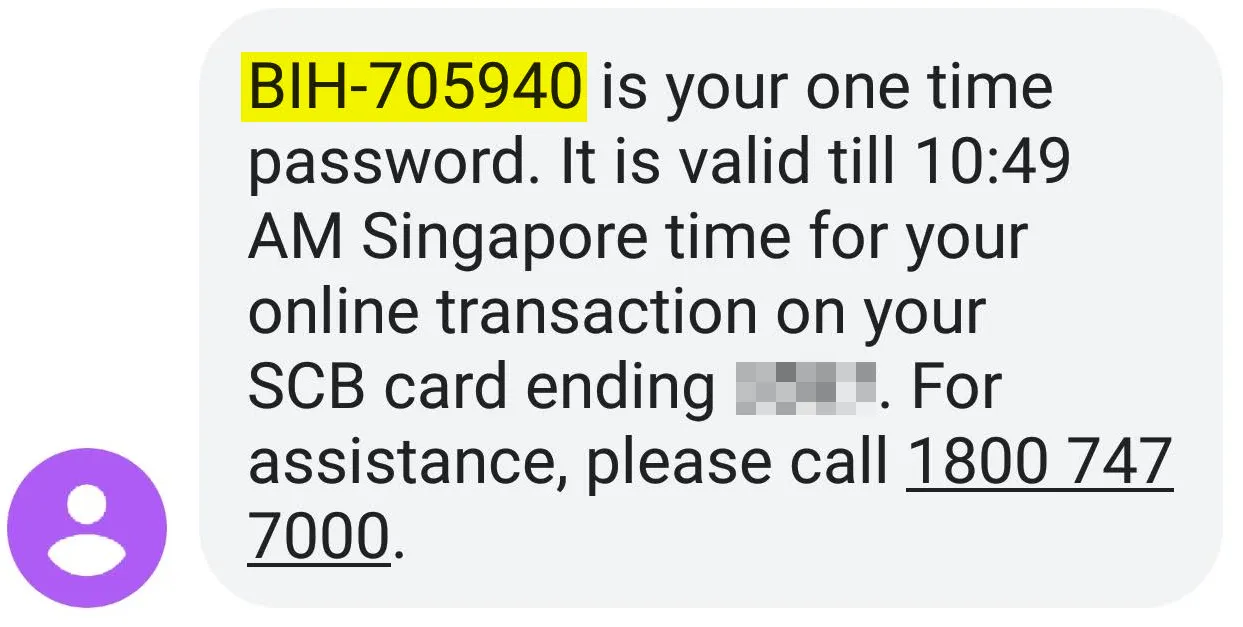
Over here, "705940" is the OTP for user to enter, and the prefix, "BIH", is a simple verification code which will also be shown on the user's screen for he/she to quickly verify that the prompt is from the correct source. Lately, more banks have also started to use mobile apps for push authorizations instead of getting users to enter the OTPs. While these are good, not all companies have the scale and funds for such implementations.
There is, however, a cheaper way to create such verification. I first get to notice this from Kucoin, a cryptocurrency trading platform. Basically, you create a login verification code with the site. The code will be displayed each time an OTP is required as such,

Screenshot from Kucoin. Verification code hidden for obvious reasons :p
This is a cheap and effective implementation. If the verification phrase is wrong, then users will immediately find that something is amiss.
Conclusion
Implementing 2FA is a security best practice and it should be a basic hygiene for most sites to have. However, implementations can be improved to provide better security for users particularly against phishing attacks that are getting increasingly prevalent. A simple verification phrase can do it, so I do not see why this cannot be implemented by more web applications. Thanks for reading and please share your thoughts. If you find this post useful, do give me a follow so that you get to see more of such in the future :).
